MalewareBytes Support tool – SAM hash dump?
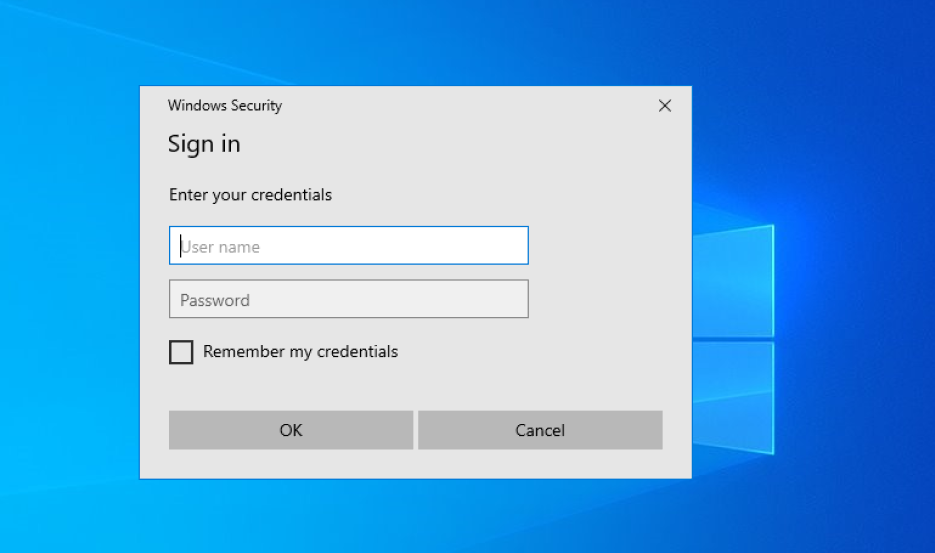
Malwarebytes provides a support tool that automatically repairs and fixes software issues and broken configurations, that’s actually common for anti-malware software to assist their customers to do that. after navigation into HelpCenter inside the Malwarebytes interface, you need to download the software package which will do self-extraction and requires elevated permission to continue running. since … Read more